Managing Cloud Security – Protection, Detection And Proactive Actions
Posted On June, 2021
Cloud security encompasses managing people, process & technology with thorough policies, that safeguard data and applications operating in the cloud. AWS allows businesses to own greater control they need to flawlessly run their operations on the strength of a powerful cloud computing environment. The vast network of data centers and network services are thoughtfully architected to safeguard confidential information, protect identities and applications across devices and platforms.
Whatever the security and compliance need, AWS protects an enterprise’s information assets and supports their top-secret workloads. By allowing them to automate manual security tasks, it frees them to focus on scaling and business innovation efforts.
In this article, we will cover different aspects of security and access management in AWS, and how Minfy as a Managed Service Provider is uniquely positioned to deliver robust security outcomes for its clients.
Security and Access Management in AWS to strengthen your cloud
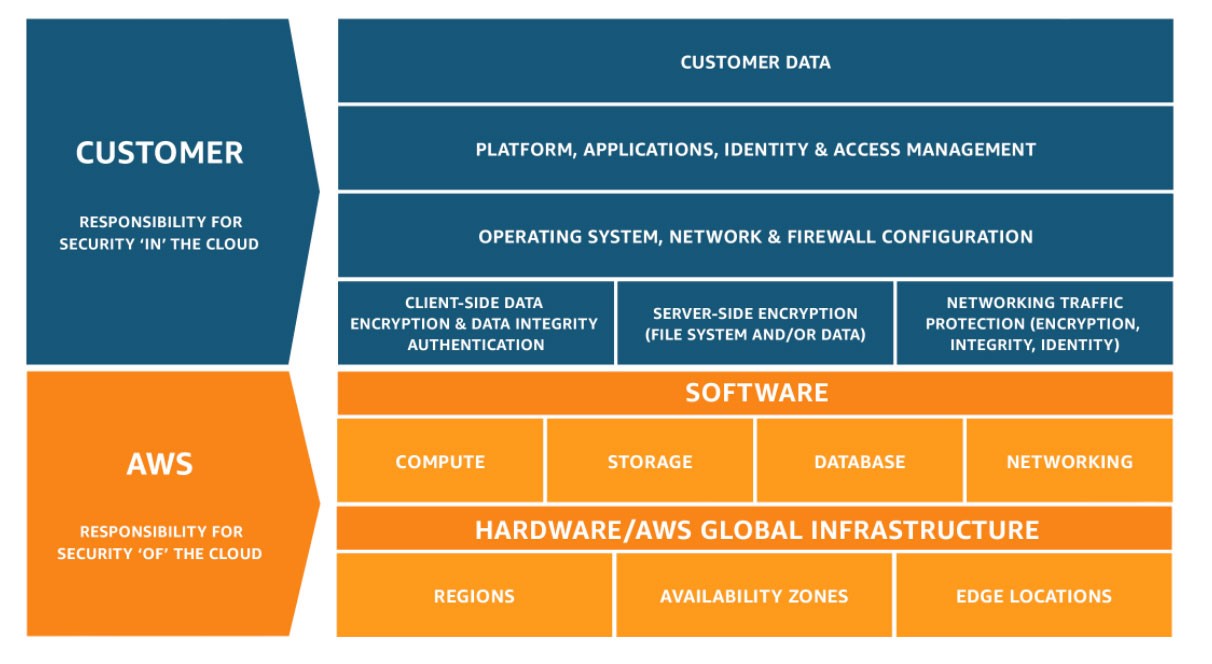
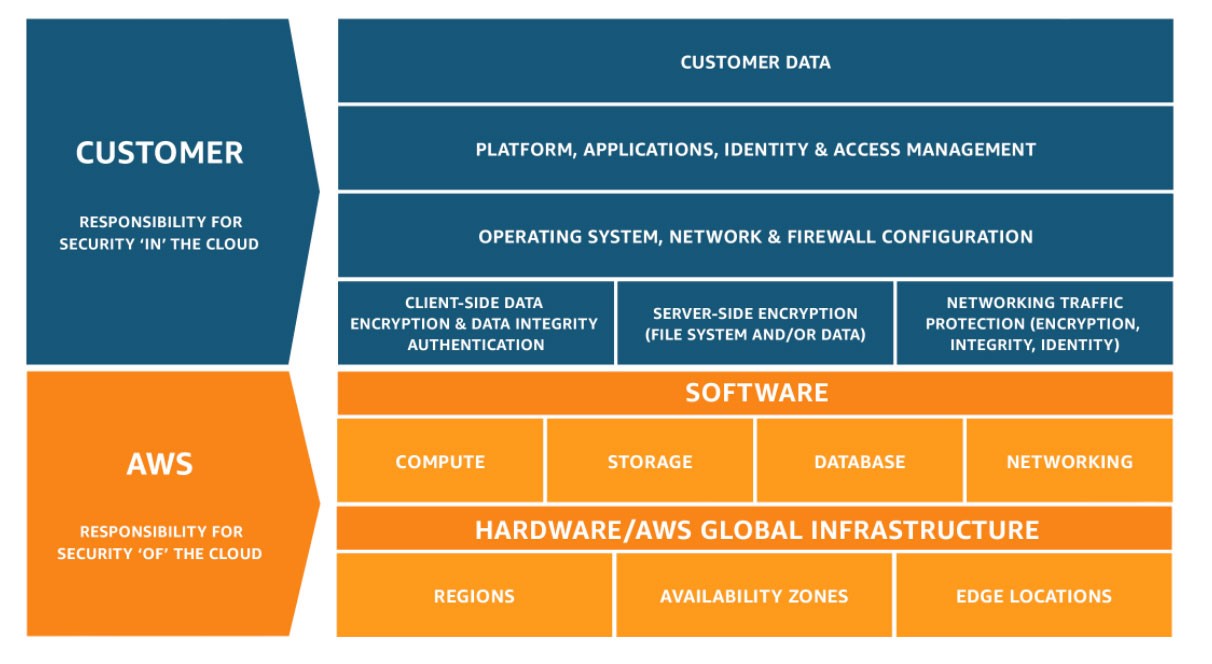
AWS maintains a shared responsibility model. This means it is responsible for the security of the underlying infrastructure leased to the customer, whereas the customer is responsible for maintaining the security of the areas in the infrastructure that they control.
Common AWS security features a business needs to power up their cloud infrastructure
IAM
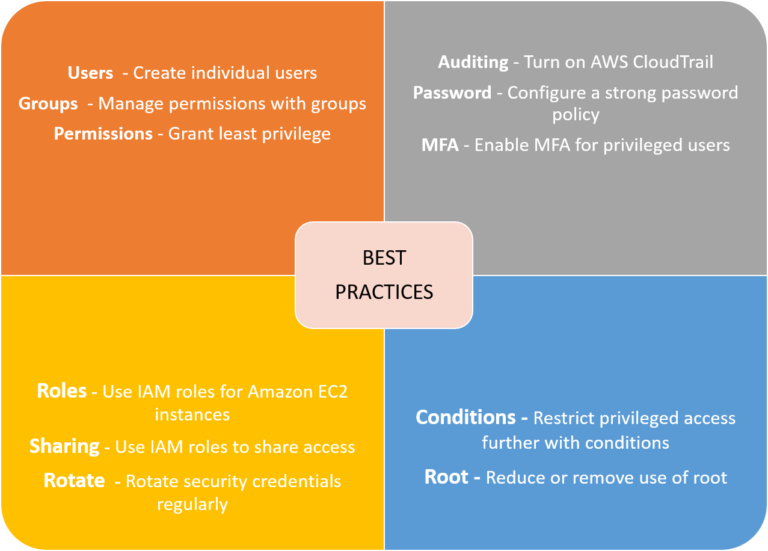
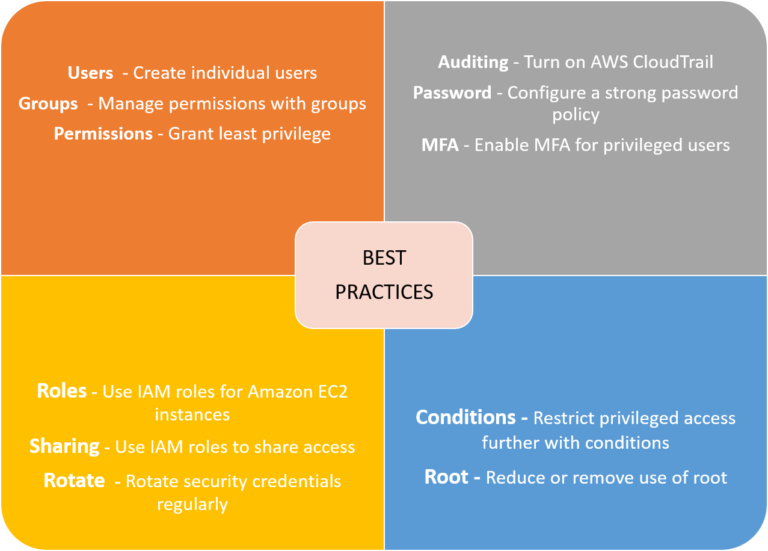
AWS Identity and Access Management (IAM) enables you to micromanage what a user can access, including services and resources. The granular level permission provides a robust security shield, letting you decide whether to allow or deny a user’s specific access rights, and which activities they can perform with the resource. You can fine grain access control by defining timing, and source of access, while setting up multi-factor authentication for highly privileged users, and refining and optimizing control rules etc.
S3 Security
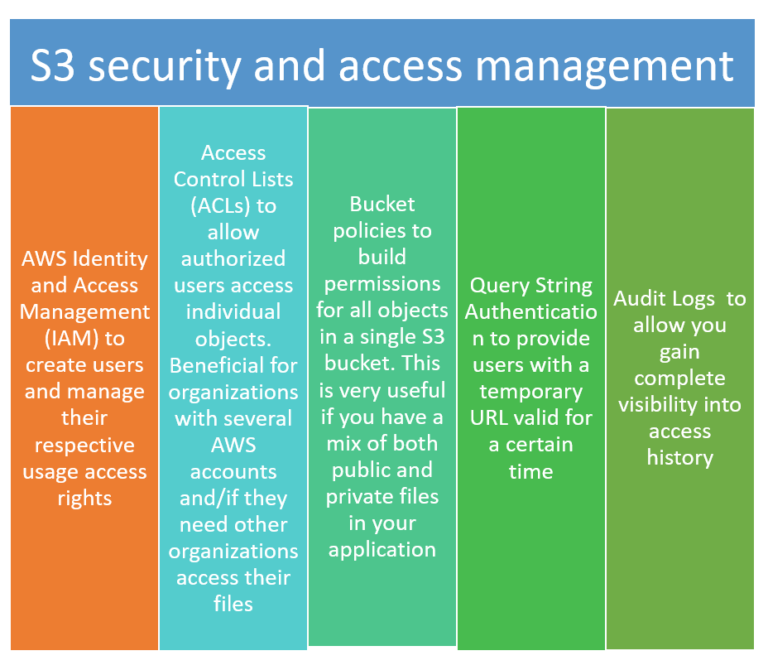
Simple Storage Service or S3 provides you with data storage with strong durability, performance, scalability and availability features. Users only have access to the S3 resources they create. There are many ways to add permissions to S3 as listed here –
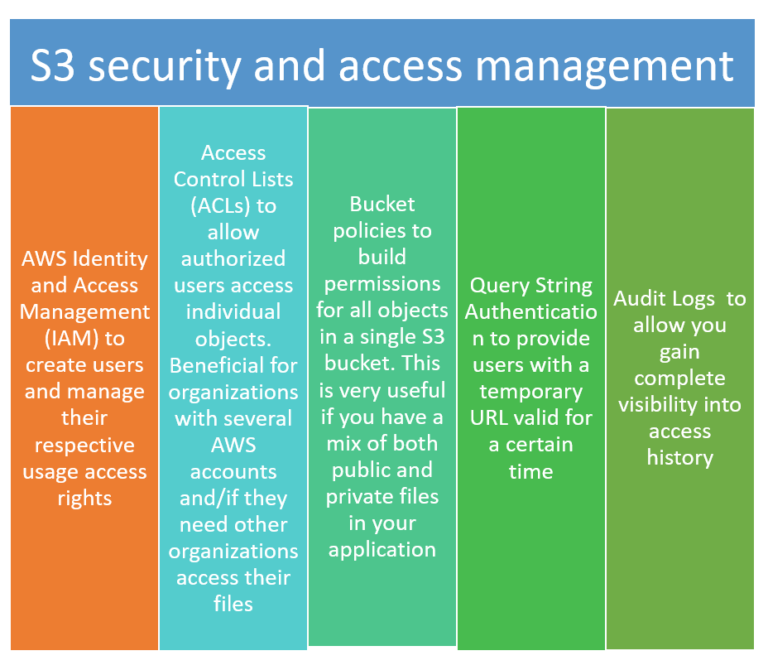
S3 empowers you to fine tune access control based on unique compliance and business needs, you can control cost depending on situational needs, and conduct large scale optimization and changes. Since it works with Lambda, logging activities, defining alerts, and managing workflows does not need managing additional infrastructure. Customers – no matter size and industry – can leverage on it to safeguard, vast amount of important data for different use cases.
Security groups
Traditional firewalls can be inflexible, and suffer from varied limiting situations. On the other hand, AWS security groups are tied with EC2 instances and offer protocol and port access level security, meaning you can spot and specify permissive rules for both inbound and outbound traffic. By default, traffic is denied, meaning if it is not explicitly allowed in, then it will automatically be rejected. Security groups are a very integral and powerful security measure in the AWS cloud.
Cloud trail
The user activity tracking tool is helpful to understand if your security configuration is robust. It enables you to gain informed insights over governance, compliance. It allows you to log, monitor, access and retain activity across your infrastructure. The capabilities when combined streamline operational tasks, and support in troubleshooting. Besides, Informed and practical visibility into user and account activity brings accountability into the process, and help resolve probable disputes before they could leave any impact.
So, using AWS, you will gain the power, flexibility and tools you need to securely run your business on the cloud. At the same time, you are in control of your enterprise’s unique and demanding security requirements.
Minfy as a Next Gen Managed Service provider with strong priorities for security
Securing IT artefacts in the cloud is not a short sprint. It is an ongoing feature of digitalized enterprises. Building cyber resilience into their systems is a priority and how well they posture against threats and risks is at the foundation of the security strategy. At Minfy we have operational experience in ensuring the perimeters of security are redrawn and the security road map details the specific customer needs.
Threat modeling and various checks and balances are part of our routine deliverables. The one aspect that distinguishes us from the others is our ability to integrate security into your day-to-day operations. In fact, seamlessly harmonize with the DevOps philosophy. When this is accomplished enterprises scan actually leverage the cloud to strengthen security parameters and be ready for eventualities.
Minfy’s security experts provide continuous protection and monitoring of its client’s digital assets on the AWS environment.
Benefits
- Well defined cyber posturing
- Security as a continuous process
- Reactive and proactive modeling
- Integration with the workflows resulting in savings of time and costs
- Reviews and audits for firm vigilance
Minfy has established proven AWS security practices, provides pro-active 24/7 support to help its clients navigate complex risks, and improves their cloud security posture. From refining security policies based on demands, setting up IR plans, vulnerability management, threat detection, responding to alerts in real time and remediating systems; Minfy closely works with its clients to make the most of their AWS experience at scale.
 Go to Swayam
Go to Swayam