- Home
- About
- Consulting
- Services
- Minfy Labs
- Industries
- Resonances
- Careers
- Contact
Securing IT artefacts in the cloud is not a short sprint. It is an ongoing feature of digitalized enterprises. Building cyber resilience into their systems is a priority and how well they posture against threats and risks is at the foundation of the security strategy. At Minfy we have operational experience in ensuring the perimeters of security are redrawn and the security road map details the specific customer needs. Threat modeling and various checks and balances are part of our routine deliverables. The one aspect that distinguishes us from the others is our ability to integrate security into your day-to-day operations. In fact, seamlessly harmonize with the DevOps philosophy. When this is accomplished enterprises scan actually leverage the cloud to strengthen security parameters and be ready for eventualities.
![]()
Enterprise view of security
Cyber resilience status
Threat and risk listing
Threat modeling
![]()
Business mapping from a security
perspective
Threats and risks inventory
Security frameworks
Preventive and causative steps
Constant reviews
![]()
Immersion into regulatory
frameworks
Comprehensive analysis of
workloads
Codification ofthe policies
Control objectives
Metrics for vigilance
![]()
Double down on the assets to the
micro level
Understand the control objectives
Enable audits and assessments
Integration with workflow tools
Catalyze automation
What is the current state?
What is the status of cyber resilience?
What is the intended cyber posturing?
How visibile are the assets - micro segmentation?
What customization is required?
What are the monitoring cycles?
What are the prevention and threat handling frameworks needed?
What are the regulatory mandatories to comply with?
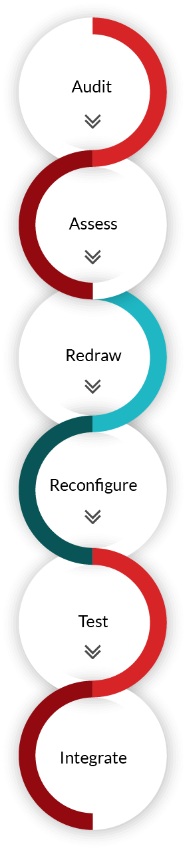

Present security goals

Prevailing security
perimeters

New perimeters

Blending prevention and
threat handling measures

Integration with workflows

Testing and shared
responsibility initiatives

Metrics and alerts

Regulatory frameworks
![]()
Costs

Well defined cyber
posturing

Security as a continuous
process

Reactive and proactive
modeling

Integrate workflows to save time and costs

Reviews and audits for firm
vigilance
Minfy leverages IP, a phased migration roadmap and a specialized team to ensure minimal downtime











© 2022 Minfy™. Minfy Technologies. All rights reserved. | Privacy Policy | Terms and Conditions
This website stores cookie on your computer. These cookies are used to collect information about how you interact with our website and allow us to remember you. We use this information in order to improve and customize your browsing experience and for analytics and metrics about our visitors both on this website and other media. To find out more about the cookies we use, see our Privacy Policy. If you decline, your information won’t be tracked when you visit this website. A single cookie will be used in your browser to remember your preference not to be tracked.
 Go to Swayam
Go to Swayam